CrowdStrike CrowdStrike Certified Falcon Hunter CCFH-202b Exam Dumps: Updated Questions & Answers (June 2026)
You identify an instance of a user in your environment utilizing a Cloudflared tunnel daemon, resulting in unusual command line activity. What steps would you take to determine if the unusual activity is malicious or legitimate?
Falcon is generating detections for a malicious file evil.exe with varying filepaths on several hosts as end users attempt to execute the file. Which query can be used to proactively hunt where the file exists prior to the user executing it?
Refer to the exhibit.
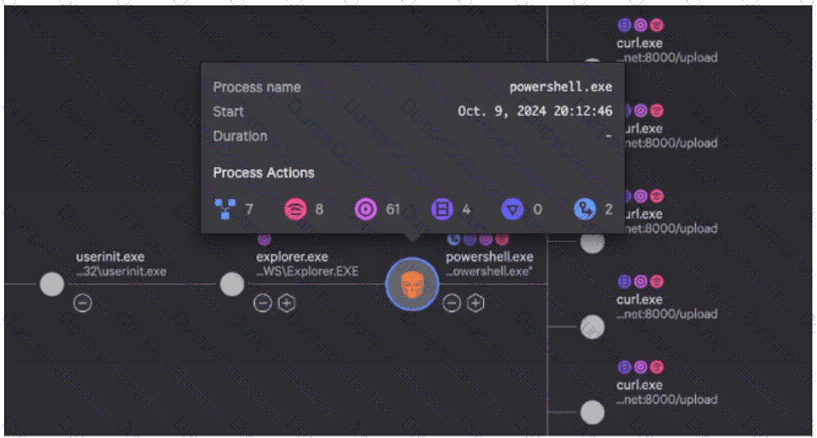
While investigating a process tree, you hover over a malicious powershell.exe process. What is the correct sequence of Process Actions?
Which hunting query's results could indicate that an adversary is performing reconnaissance from a specific host?
Refer to the image. Which query will show file execution from a suspicious directory across all hosts?
Your organization has identified a malicious Scheduled task that executes every 5 minutes. Which LogScale event search function can be used to quickly identify and display the unique hosts affected by the malware?
What is the expected result of this CQL query?
#event_simpleName=UserLogon RemoteAddressIP4=* | !cidr(RemoteAddressIP4, subnet=["224.0.0.0/4", "10.0.0.0/8", "172.16.0.0/12", "192.168.0.0/16", "127.0.0.0/8", "169.254.0.0/16", "0.0.0.0/32"]) | ipLocation(field=RemoteAddressIP4, as="ip")
Which field in a DNS Request event points to the responsible process?
When will the ContextProcessId be the same value as the TargetProcessId?
Where can you find details about key data fields to use in an advanced search query?

