ECCouncil Certified SOC Analyst (CSA v2) 312-39 Exam Dumps: Updated Questions & Answers (June 2026)
Harley is working as a SOC analyst with Powell Tech. Powell Inc. is using Internet Information Service (IIS) version 7.0 to host their website.
Where will Harley find the web server logs, ifhe wants to investigate them for any anomalies?
An organization is implementing and deploying the SIEM with following capabilities.
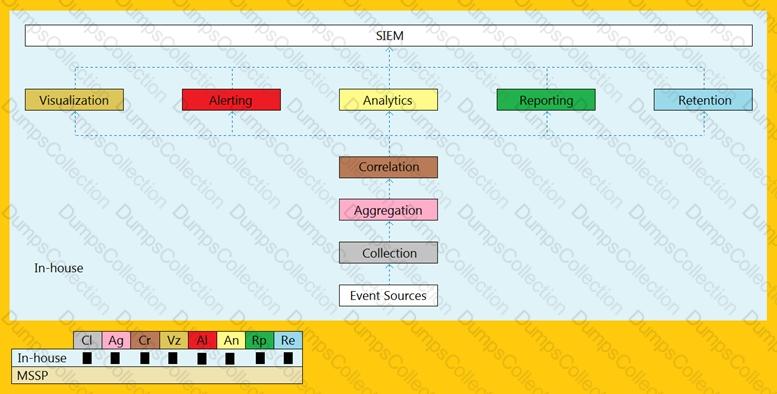
What kind of SIEM deployment architecture the organization is planning to implement?
Which of the following framework describes the essential characteristics of an organization's security engineering process that must exist to ensure good security engineering?
Which of the following stage executed after identifying the required event sources?
What does the HTTP status codes 1XX represents?
Which of the following technique involves scanning the headers of IP packets leaving a network to make sure
thatthe unauthorized or malicious traffic never leaves the internal network?
Which of the following fields in Windows logs defines the type of event occurred, such as Correlation Hint, Response Time, SQM, WDI Context, and so on?
Which of the log storage method arranges event logs in the form of a circularbuffer?
Which of the following formula represents the risk?
Which of the following event detection techniques uses User and Entity Behavior Analytics (UEBA)?

