Fortinet Fortinet NSE 5 - FortiSASE and SD-WAN 7.6 Core Administrator NSE5_SSE_AD-7.6 Exam Dumps: Updated Questions & Answers (April 2026)
You have a FortiGate configuration with three user-defined SD-WAN zones and one or two members in each of these zones. One SD-WAN member is no longer used in health-check and SD-WAN rules. This member is the only member of its zone. You want to delete it.
What happens if you delete the SD-WAN member from the FortiGate GUI?
Refer to the exhibit.
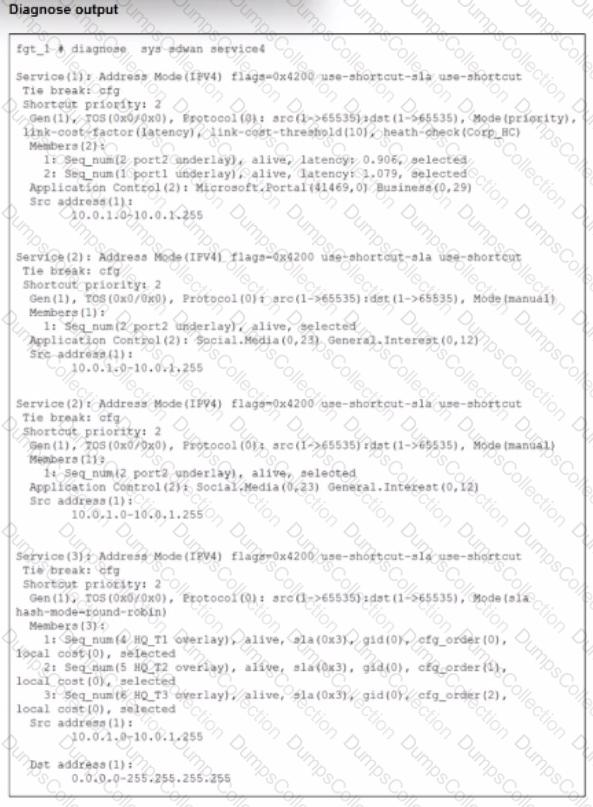
The exhibit shows output of the command diagnose sys sdwan service collected on a FortiGate device.
The administrator wants to know through which interface FortiGate will steer traffic from local users on subnet 10.0.1.0/255.255.255.192 and with a destination of the social media application Facebook.
Based on the exhibits, which two statements are correct? (Choose two.)
Which three authentication sources support secure identity verification and access control for FortiSASE remote users? (Choose three.)
Which configuration is a valid use case for FortiSASE features in supporting remote users?
Refer to the exhibits.
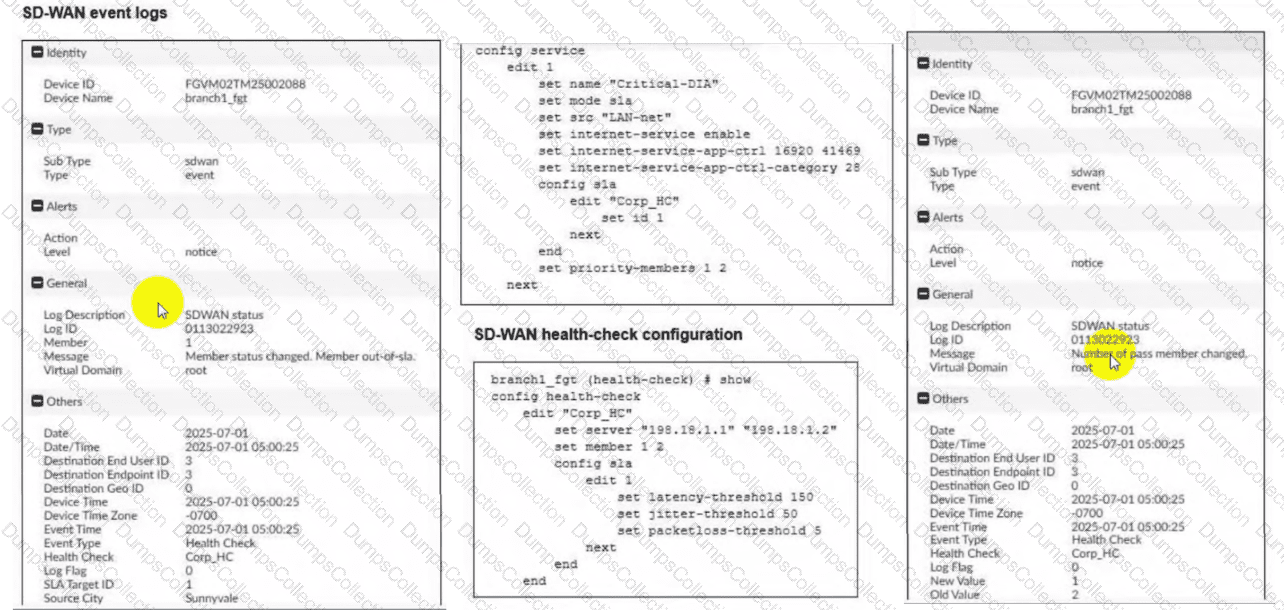
Two SD-WAN event logs, the member status, the SD-WAN rule configuration, and the health-check configuration for a FortiGate device are shown. Immediately after the log messages are displayed, how will the FortiGate steer the traffic based on the information shown in the exhibits? (Choose one answer)
Which two statements correctly describe what happens when traffic matches the implicit SD-WAN rule? (Choose two answers)
What is a key use case for FortiSASE Secure Internet Access (SIA) in an agentless deployment? (Choose one answer)
Which three FortiSASE use cases are possible? (Choose three answers)
Which statement is true about FortiSASE supported deployment?
You want FortiGate to use SD-WAN rules to steer ping local-out traffic. Which two constraints should you consider? (Choose two.)

