Huawei HCIA-Security V4.0 Exam H12-711_V4.0 Exam Dumps: Updated Questions & Answers (June 2026)
Social engineering is a means of harm such as deception, harm, etc. through psychological traps such as psychological weaknesses, instinctive reactions, curiosity, trust, and greed of victims ( )
Using the ___ method of the Web proxy, the virtual gateway will encrypt the real URL that the user wants to access, and can adapt to different terminal types.[fill in the blank]*
An engineer needs to back up the firewall configuration. Now he wants to use a command to view all the current configurations of the firewall. May I ask the command he uses is ____[fill in the blank]*
As shown in the figure, the administrator needs to test the network quality of the 20.0.0/24 CIDR block to the 40.0.0/24 CIDR block on Device B, and the device needs to send large packets for a long time to test the network connectivity and stability.

Which of the following is not an application scenario for PKI?
In asymmetric encryption algorithms, only public keys can be used to encrypt data, and private keys are used to decrypt data. This process is irreversible.
Compared with the software architecture of C/S, B/S does not need to install a browser, and users are more flexible and convenient to use.
The network environment is becoming more and more complex, and network security incidents occur frequently. While accelerating the construction of informatization, enterprises must not only resist external attacks, but also prevent internal management personnel from being involved in data leakage and operation and maintenance accidents due to operational errors and other issues. Which of the following options might reduce operational risk?
Which of the following is not the matching mode of the firewall security protection whitelist rules?
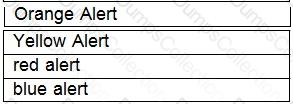
Drag the warning level of the network security emergency response on the left into the box on the right, and arrange it from top to bottom in order of severity.[fill in the blank]*