Proofpoint Certified Threat Protection Analyst Exam PPAN01 Exam Dumps: Updated Questions & Answers (May 2026)
An analyst has been tasked with providing a report that can be used to prioritise investigations based on a user's Attack Index score. Which report would be most suitable for this purpose?
What is a defining characteristic of Advanced Persistent Threat (APT) actors?
What is the first action a security analyst should take when beginning to review and prioritize alerts from Targeted Attack Protection (TAP)?
Which Proofpoint product quarantines malicious email after delivery?
Exhibit:
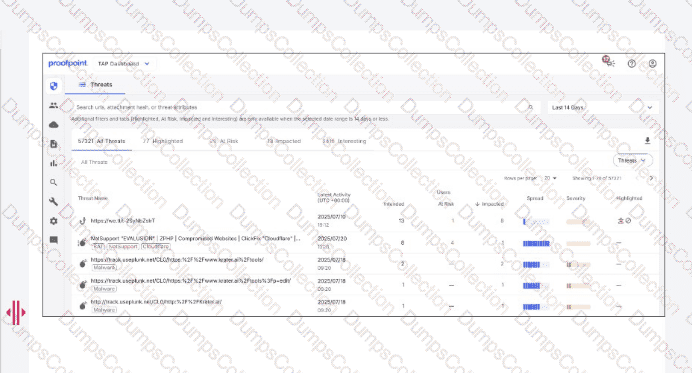
Which column indicates the number of users targeted by a malicious campaign or threat?
Which TAP condemnation results from an analysis of emails submitted via Proofpoint ZenGuide Report Suspicious (formerly PhishAlarm)?
Which two tasks are considered frequent and high-priority when actively reviewing the threat landscape? (Select two.)
An analyst is reviewing a quarantined threat within Threat Protection Workbench.
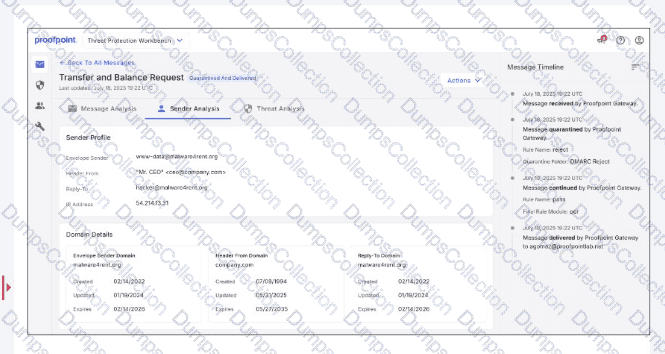
Based on the indicators shown in the exhibit, what is the most likely reason the threat was quarantined?
As a new analyst, you need to review threat intelligence related to threats in your environment. Which Proofpoint product provides this data?
An analyst wants to use the Threats page in TAP Dashboard to review all messages related to a phishing campaign that contain an attachment. What is the correct method to filter these messages?

